CSAW 2017 Missed Registration Writeup
This is a writeup of the Missed Registration challenge at CSAW 2017.
This is a forensics challenge worth 150 points.
We are given a pcap file to analyze. After opening it up in Wireshark, we can follow the TCP streams to get a feel of what's going on.
Browsing through the streams, we notice there is a lot of HTTP traffic for school registration. The requests are mostly the same with random fields for names, schools, and courses. The responses all appear to be the same.
Briefly looking at the other traffic in the pcap suggests there is not anything else too interesting for this challenge. The challenge description mentions registration and these forms, so it's very likely the answer is in this HTTP traffic somewhere.
Since the responses all appear the same, let's focus on the requests. The headers change slightly for some of the requests. Most of the requests have these headers:
POST / HTTP/1.1
Host: 192.168.0.21:8080
Connection: keep-alive
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: python-requests/2.11.1
Content-Length: 506
Content-Type: application/x-www-form-urlencoded
While some of the requests have these headers.
POST / HTTP/1.1
Host: 192.168.0.21:8080
Accept-Encoding: identity
Content-Length: 493
Content-Type: application/x-www-form-urlencoded
Basically, one request is asking for compression and one isn't. This could be something of note, but these headers don't contain the flag, so we can go back to it later.
Switching over to the values in the request, we see "n" and "s". The former is a long string of hex values and the latter is a single letter from A-F. I think the latter could be for grades. At this point I thought the flag must be in "n", but then I noticed that there was an "x" value in certain requests, those with the "Accept-Encoding" header of "identity."
The hex values for "n" and "x" did not decode into ASCII. What else could they be? Well, there are enough values for a small file, so we can try looking for that.
I need to extract these values together into a file, turn them into a binary, and then use a tool like foremost to identify any potential files.
I used the following command to extract the values cleanly:
strings cap.pcap | grep -o -f expression | sed 's/&x=//g' | tr -d '\n' | sed 's/[^A-Fa-f0-9]//g' > output.txt
where "expression" is a file with contents (here, it's "x", but it could be "n" as well):
&x=.*
Broken down, strings is grabbing the text of the pcap, grep is only extracting content that matches the regular expression in the file "expression," which is just the value syntax "&x=" followed by a regular expression, ".*", to match whatever comes after that syntax. Next, sed is removing the value syntax, "&x=", tr is removing new lines, and sed is removing any non-hex values.
To convert these hex values from a string to values in a binary, we can use a short Python script.
string_hex_file = open("output.txt", "r")
hex_as_string = string_hex_file.read()
hex_as_binary = hex_as_string.decode("hex")
binary_hex_file = open("binary", "w+")
binary_hex_file.write(hex_as_binary)
string_hex_file.close()
binary_hex_file.close()
We simply open our output file, read the bytes as hex, and write them to a new file.
Now, we can use a tool like foremost to extract any files that might be in there.
root@kali:/opt/ctf/csaw17# foremost -i binary
Processing: binary
|*|
It looks like it found a bmp file, which could be an image with the flag. Let's check it out!
root@kali:/opt/ctf/csaw17/output# ls
audit.txt bmp
root@kali:/opt/ctf/csaw17/output# ls bmp
00000000.bmp
root@kali:/opt/ctf/csaw17/output# eog bmp/00000000.bmp
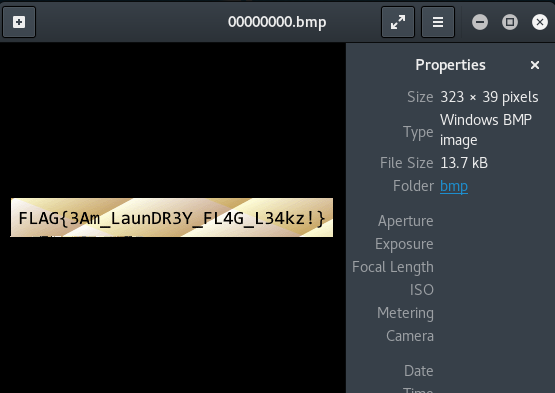
Success!
It was pretty apparent quickly that the flag was likely somewhere in the HTTP requests, but it took time to spot the "x" value (since it was only in some requests and somewhat hidden after the "n value") and then to realize there could be a file header inside. Overall, this was a fun and interesting challenge.